Security Operations for the AI Age
Collaborating agents and analysts.
Faster investigations and consistent outcomes via shared tools, data and knowledge.
.svg)





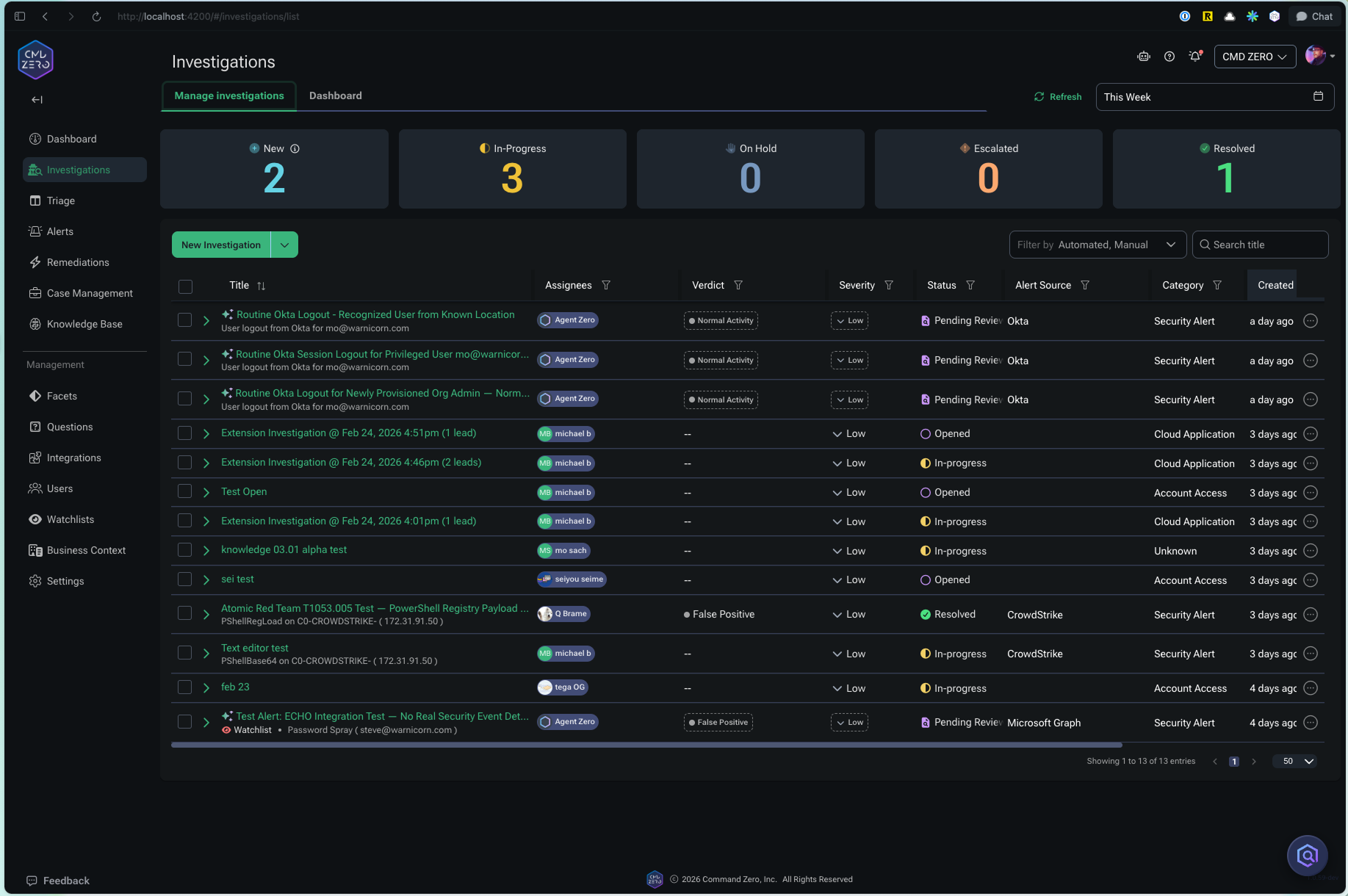
Alert to response in seconds.
Launch every case with deep expert knowledge and pre-built playbooks.
1. Connect in minutes.
Link your existing stack via read-only APIs. No data migration. No ingestion pipeline. No reconfiguration of tools.
Endpoint. Identity. Cloud. Email. SaaS. SIEM. All available for questions.
Most customer environments go live in under an hour.

2. Questions lead to answers.
Every investigation — autonomous or analyst-led — draws on an encoded knowledge base of high-impact questions built by Command Zero's research team.
Expert questions define what the platform looks for, what data it queries, and how it reasons. They are the building blocks of every investigation.
Your team can add their own questions, import detection logic from existing platforms, and build custom investigation flows. All of it is available to every analyst and every AI agent.
No training period. No cold start. Expert-level analysis on day one.

3. Augment SOC capabilities.
Autonomous, AI-assisted, or both. Command Zero adapts to your team's workflow and alert type.
Autonomous investigations
AI agents take in an alert, investigate across connected data sources, document every step, and deliver a verdict with supporting evidence. Analysts review, not rebuild them.
AI-assisted investigations
For escalated cases, threat hunts, and bespoke scenarios, analysts work alongside agents. Get follow-up questions, pull data across systems, and generate timelines automatically.
Human-led investigations
Senior analysts and threat hunters can work with full data access and expert content. Every step is logged and reusable.
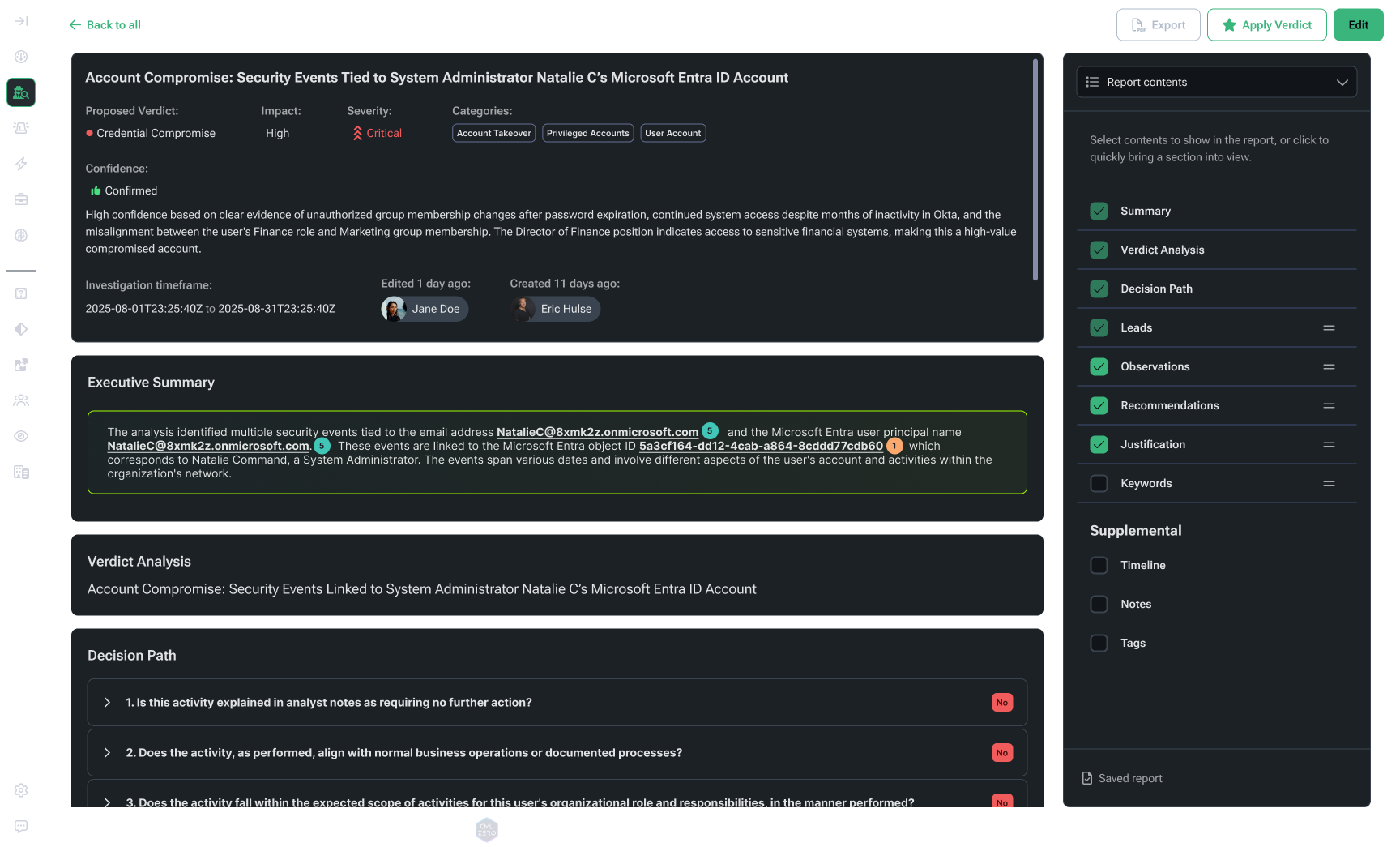
Governed AI. Question-based method.
Most AI SOC solutions provide an answer and hide the how/reasoning. Command Zero delivers control, visibility and deterministic outcomes with questions.
See every single step: Every question the agent asked, every data source, and every piece of evidence.
This transparency is what makes agents trustworthy in security operations — and defensible to your leadership.
How the question-based architecture works:
Command Zero ships proven high-impact questions.
Built by our research team. Updated as threats evolve. Every question maps to a specific data source, a specific query, and a specific investigative intent.
Questions serve as building blocks for every analysis.
Whether an agent runs an investigation or a human analyst does, they use the same questions. Every step is visible, auditable, and reproducible.
Add your own questions and data sources.
Import detection logic from existing platforms like Splunk and CrowdStrike Next-Gen SIEM. Build custom questions for your environment including custom data sources. Uplevel agents and analysts.
Agents only use available questions.
Know exactly what your agents are capable of asking. Control and expand the scope on your terms.
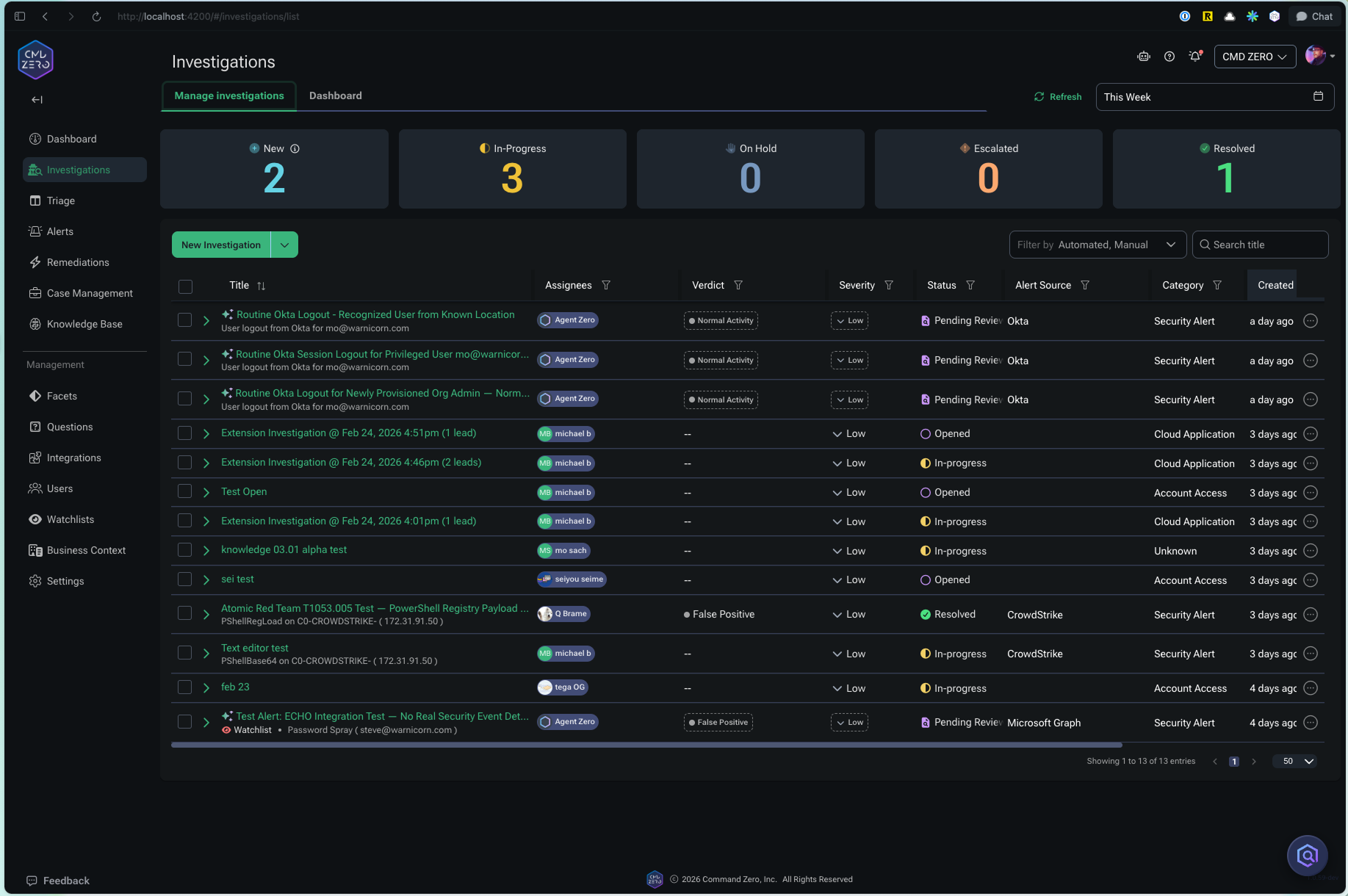
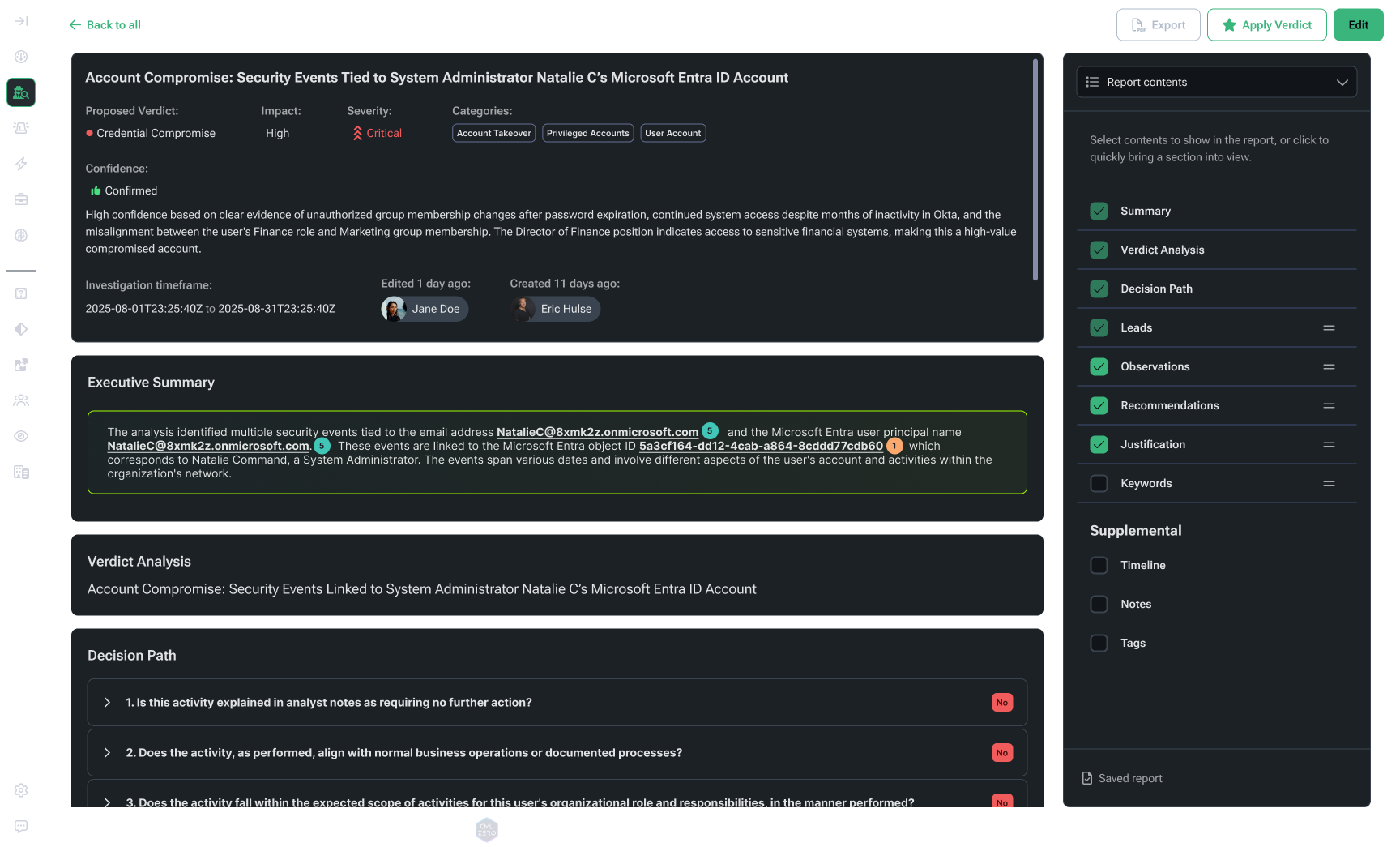
Reports: Less writing, more doing
When an investigation closes, Command Zero generates a complete report automatically. No manual write-up. No timeline reconstruction.
Verdict with supporting evidence.
Every data point that drove the conclusion. Every source queried. Every question asked and answered.
Full narrative across the environment.
Not just the original alert — the complete picture of what it means across identity, cloud, endpoint, email, and beyond.
False positive analysis.
Tests run to rule out benign explanations. What was considered and discarded, with reasoning.
Business context.
Environmental details that shaped the investigation — watchlists, enrichment data, prior investigation history.
Tier-1 analysts get what they need to close or escalate.
Tier-2 and Tier-3 get the full IR-level package — logs, timelines, complete chain of evidence.
.png)

.png)

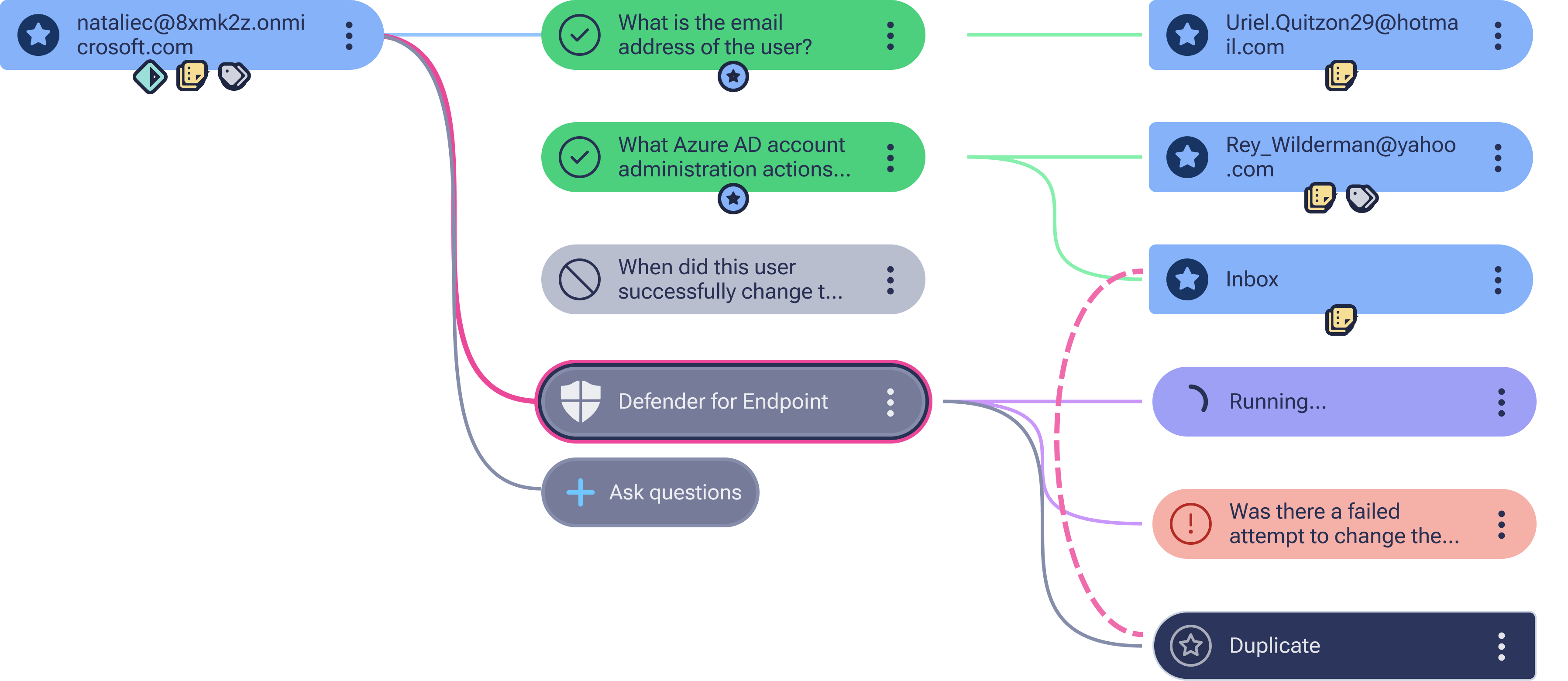
Automated Investigations. Stop routing alerts — start closing them. Command Zero autonomously investigates every Tier-1 case with the structured reasoning of a senior analyst. It delivers a complete, auditable verdict before a human touches the alert.
Investigate anything across data sources.
No ingestion pipeline.
No painful data migration. No new storage costs. No waiting for data to land in a store before you can investigate it.
Longer lookback. More context.
Query historical data from the SIEM, data lake or original data source. Combine active state information with historical records for a complete picture.
Investigate the full stack.
Endpoint. Identity. Cloud. Email. SaaS. Custom data sources. Follow the threat wherever it leads — across every system, in a single investigation.
Leverage SIEMs and data lakes.
Command Zero complements centralized data stores — it doesn't require you to replace them. Query your SIEM alongside direct data sources in the same investigation.
Frequently asked questions
Most AI SOC tools give you an answer and hide the reasoning.
Who is Command Zero built for?
Mid-to-large and very large enterprises with in-house security operations teams. If you have analysts investigating cases (whether that's a five-person team or a two-hundred-person global SOC) Command Zero is built for you.
The platform serves analysts at every tier. Tier-1 analysts benefit from autonomous investigation and noise reduction. Tier-2 and Tier-3 analysts get faster data access, AI assistance on complex cases, and better tools for reporting. SOC managers get consistent outcomes and measurable metrics.
How is Command Zero different from AI SOC agents?
Most AI SOC agents focus on tier-1 triage. They're good at deciding whether to escalate. They're not built for what comes after.
Command Zero handles the full investigation lifecycle — from alert intake through complex multi-source analysis to case closure. The AI doesn't just triage; it investigates. And when a case exceeds what the AI should decide alone, it hands off to a human analyst with full context intact.
How does it work with our existing tools?
Command Zero connects to your existing stack via read-only API connections. It doesn't replace your SIEM, EDR, or identity tools — it extends them. Investigate data from all of them in a single, unified investigation.
SIEM integration is supported alongside direct data source access. You can query both in the same investigation.
How long does it take to deploy?
Most environments are live in under an hour. No data migration. No playbook setup required before you start. Expert investigation content is available from day one.
Does it require setup before it's useful?
No. Expert-level investigation content ships with every deployment — pre-built questions, investigation plans, and detection logic from Command Zero's research team. It's ready on day one.
The content updates continuously as threats evolve. Your team doesn't maintain it.
How does the platform get smarter over time?
Every investigation adds to the knowledge base. Enrichment data, analyst annotations, and prior investigation context accumulate across cases. The more you use it, the more accurate it gets.
When senior analysts build better investigation approaches, that logic is captured as reusable questions and plans. It doesn't leave when they do.
How do AI agents and human analysts work together?
The agent completes its investigation and hands off with everything intact — full context, all artifacts, complete decision trail. The analyst picks up exactly where the agent left off. No rework. No lost context.
Analysts can take over, extend, or redirect any autonomous investigation. Add new questions, pivot to new data sources, or direct the agent to reconsider its verdict based on new evidence. Teams can also collaborate on the same case — sharing notes with each other and with the AI agent.
What metrics does Command Zero surface?
The ones SOC leaders actually care about: escalation rates, mean time from alert to closed case, and analyst efficiency by case type.
You can also replay past investigations — review what the agent did and why. Useful for training new analysts and improving investigation content over time.
How is the platform licensed?
Licensing is based on your environment and security operations team. Contact us for details.
Is there a free trial?
We offer a proof-of-value engagement — an assisted trial with our team. Contact us or book a demo to get started.
See what your team can do with Command Zero
Live in under an hour.
No migration.
No setup.
