AI agents turn Tier-1 from a routing desk into a resolution engine —
investigating every alert with the structured reasoning of a senior analyst.


Tier-1 is breaking. Too much noise.
Not enough time. No scalable way out.
of SOC budget goes to Tier-1 triage.
of alerts are never investigated.
of analysts burn out—and leave within 12–18 months.
Autonomous investigations. Full context. Zero guesswork.
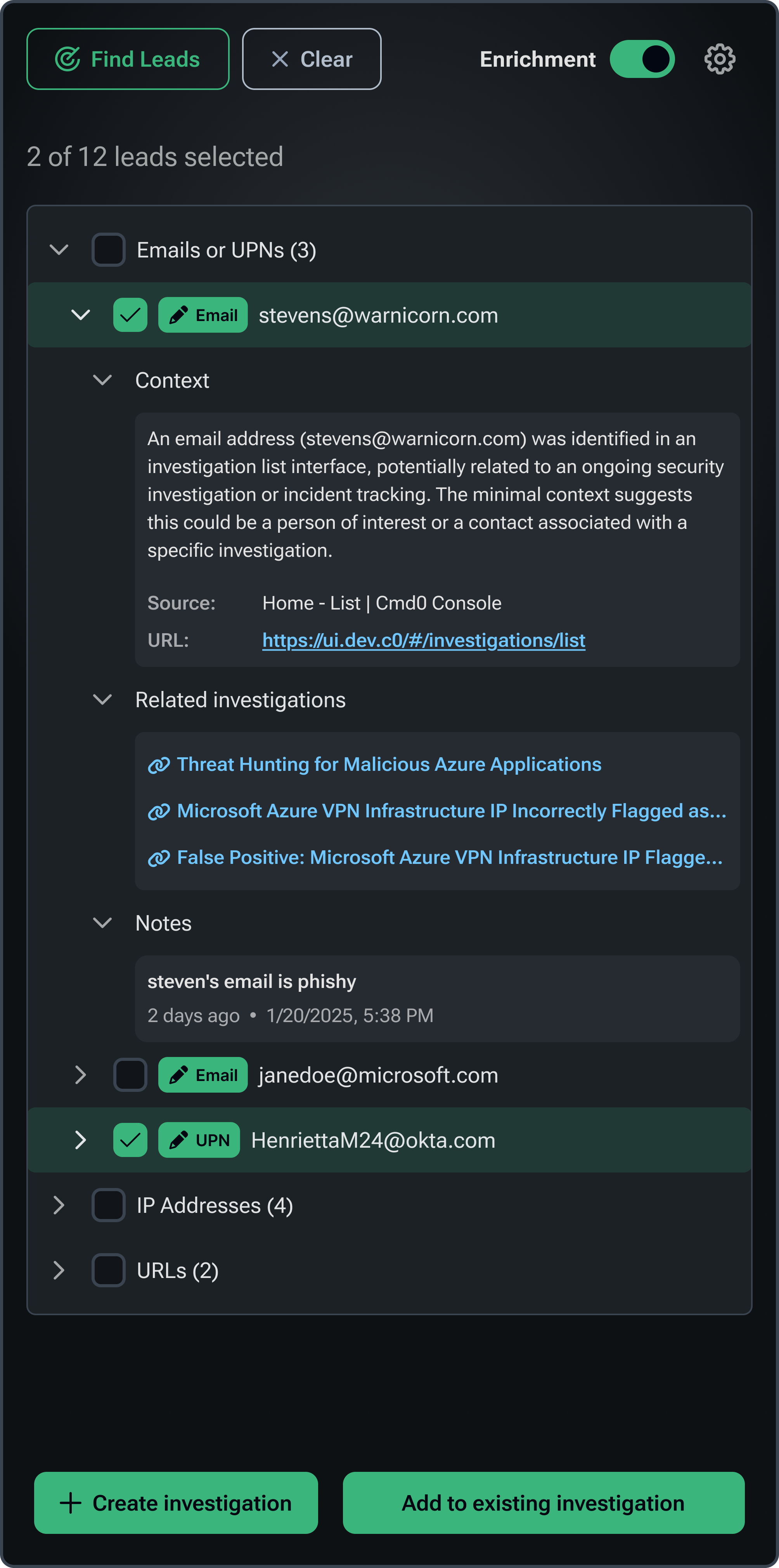
Command Zero ingests, enriches, and investigates every alert—end to end.
It doesn’t return a score.
It delivers a verdict with evidence.
What’s different:
• Glass-box reasoning — every step is visible
• Q&A investigation engine — mirrors senior analyst thinking
• Full audit trail — every question, every answer, documented
No black boxes.
No blind trust.
Just verified outcomes.
From alert to verdict in minutes.
Complete investigation.
Ready to act.
Before a human even opens the case.
Manual triage. Tool hopping.
Delays. 30–60 minutes—if it gets touched.
Command Zero correlates everything automatically:
email → URL detonation →
identity logs → endpoint activity → lateral movement
Indicator extraction, sandboxing, identity correlation.
Hash validation, threat intel matching, automated containment.
Brute force, MFA fatigue, suspicious access mapping.
Misconfigurations, crypto mining signals, automated response.
Request a custom Total Economic Impact (TEI) assessment—and quantify what autonomous investigations unlock in your environment.
BOOK A DEMODirect-to-data access & SIEM support.
Start in under an hour.
Unify investigation for all tools.
Scale shared knowledge.
Uplevel humans and agents.