Operationalizing threat intelligence at scale: Challenges and solutions
The Command Zero experience vs. legacy investigation flows

Introduction
Threat intelligence is one of the main building blocks for effective security operations. It provides the historical context needed to make sense of alerts, logs, and potential threats. But operationalizing it is hard in tactical terms. Security operations teams face three major challenges: consistency, volume, and actionability. In this post, we break these down and explore how Command Zero helps solve them.
Why is threat intelligence important for SecOps?
Threat intelligence provides a current and historical account of what’s happening in the available public and non-public intel resources. It offers context for alerts, logs, and other security data, enabling teams to make sense of potential threats. Threat intelligence comes in various forms—atomic (specific indicators like IP addresses or hashes) and behavioral (patterns of attack). These categories help security teams understand what to look for and how to piece together the puzzle of an attack.
As potent as it is, threat intelligence isn’t one-size-fits-all. Different industries have unique needs, and specialized intelligence—such as that provided by companies like Dragos for critical infrastructure and IoT, or specialized vertical-focused intel curated by ISAC groups—can be crucial for tailored defense strategies.
Common challenges of operationalizing threat intelligence
While threat intelligence is invaluable for all organizations, operationalizing it is no small feat. Common key challenges include:
- Consistency Across Teams: Getting every analyst in an organization on the same page is difficult. Different analysts may interpret and apply threat intelligence in varying ways, leading to inconsistencies in how threats are addressed. The result may be a false sense of security or unwarranted paranoia, both destructive patterns for managing overall risk.
- Volume and Prioritization: The sheer volume of threat intelligence can be overwhelming. Security operations teams must sift through vast amounts of data to determine what’s relevant, applicable, and timely. Historical intelligence, while useful, may no longer be relevant if the organization’s or the threat actor’s infrastructure has already changed.
- Actionability: Once the intelligence is prioritized for the organizational context, the next challenge is effectively putting it into action. How do you take atomic or behavioral indicators and systematically apply them across your organization? And how do you scale this process to handle the volume of data?
How Command Zero helps overcome common challenges
Command Zero is designed to address these pain points head-on by operationalizing threat intelligence at scale. By using pre-built content and execution paths paired with expert LLMs, Command Zero enables security teams to quickly act on threat intelligence without the need for complex queries or manual investigations.
- Atomic Indicators: Command Zero allows teams to load atomic indicators and execute single-point questions across all integrations. For example, if you have a list of malicious domains or IPs, you don’t need to write complex queries for your SIEM. Instead, you can quickly search across your environment to see if any systems are communicating with those indicators.
- Behavioral Intelligence: We apply MITRE ATT&CK labels and categories to our questions, enabling teams to start with a broad lens and drill down into specific behaviors. This is particularly useful when dealing with sophisticated threat actors who adapt their tactics. For instance, if a threat actor is known for using Living-off-the-Land (LotL) techniques, Command Zero can help identify similar behaviors across your environment, even if the specific tools or commands have changed.
- Proving or Disproving Potential Threats: One of the most time-consuming aspects of threat intelligence is proving or disproving a potential threat. Command Zero’s automated alert investigations and systematic flows allow teams to quickly validate whether a threat is real.
For example, if an S3 bucket is exposed on the dark web, Command Zero can automatically investigate:
- Who has accessed the bucket?
- Were there any unauthorized accesses?
- What actions were taken?
This process is automated, so analysts don’t have to manually comb through logs. The platform does the heavy lifting, allowing teams to focus on high-value decision-making activities.
Real-World use case examples
Here are some specific examples of how Command Zero operationalizes threat intelligence, based on some of our recent customer engagements. While it is sexy for any security tool to find a threat in progress, Command Zero excels at helping analysts navigate the day-to-day analysis – mostly consisting of disproving malicious activity:
1. Exposed S3 bucket in the Dark Web
A customer discovered an S3 bucket exposed on the dark web. Using Command Zero, they quickly initiated an investigation to determine:
- Who had access to the bucket?
- Were there any unauthorized accesses?
- What actions were taken?
The investigation revealed that only known corporate entities had accessed the bucket, and no unauthorized activity had occurred. This entire investigation took five minutes, not hours.
2. Leaked infrastructure key
A GitHub key was accidentally exposed due to a misconfigured policy. Command Zero automatically triggered an investigation to assess the impact:
- What access did the key have?
- What actions were taken with it?
- Were there any policy violations?
The investigation showed that the key had limited access and no malicious activity had occurred. The team was able to quickly revoke the key and update their policies.
3. Exposed user credentials in a breach:
A user’s credentials appeared in a breach. Command Zero automatically investigated:
- When was the password last reset?
- What were the login locations?
- Was there any suspicious activity?
The investigation confirmed that the account wasn’t compromised, but the password needed to be reset. The entire process was automated, saving the team valuable time.
During the investigation, the analyst team branched out to find similar patterns and discovered two users who were indeed compromised. The team took immediate action to stop this active threat as a result.
This example demonstrated one of the top qualities of the Command Zero platform: flexibility. Investigations may start with a certain hypothesis, yet analysts have the freedom and speed to dig into patterns of interest as they go. The platform makes it easy to branch out into similar patterns, chase evidence through rabbit holes without getting lost or drifting from the initial goal.
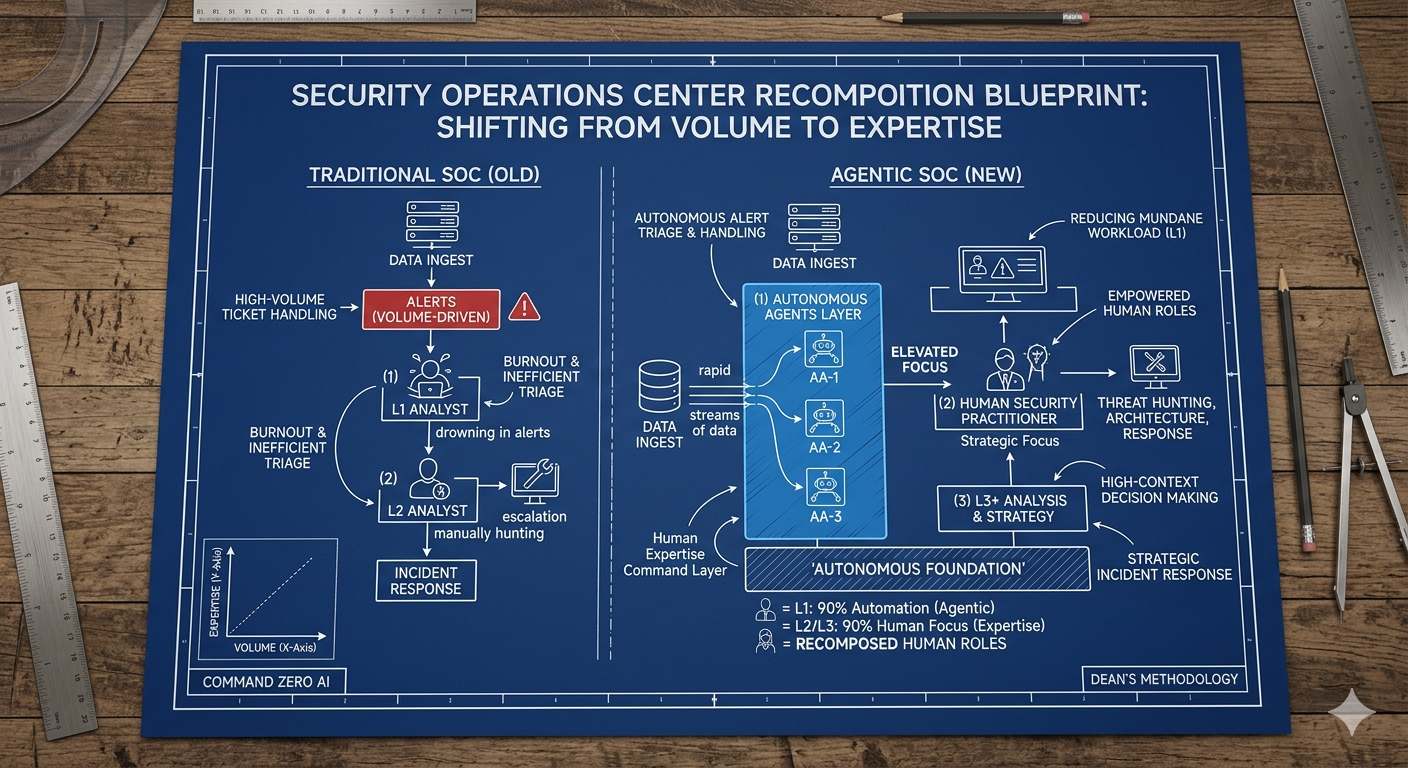
The Command Zero experience vs. legacy investigation flows
SIEM/SOAR alerts and queries are common places for investigations to start, yet complex analyses often require thorough data residing at multiple data sources. As a result, most SOC tier-2+ analysts waste cycles console switching and context switching, which can lead to inefficiencies and errors. Command Zero streamlines these processes by centralizing investigations and providing a unified platform for threat intelligence.
In one recent example, one of our customers was able to replicate 92% of a 50-minute investigation across seven different products in just 3 minutes using Command Zero. The analyst who went through both flows noted that it took longer to log into each individual product console for the analysis than it did to complete the investigation using Command Zero.
In short, analysts can reach defendable conclusions for complex cases and document analysis outcomes in minutes using Command Zero.
Nurturing collaboration and continuous improvement
The advanced investigation process has been a lonely endeavor – often relying on a single individual’s unique expertise, availability and focus to drive cases to closure. This approach limits opportunities for cross pollination and learning across analysts, leaving organizations exposed to staffing risks.
One of Command Zero’s standout features is its ability to document every step of an investigation transparently. This not only facilitates collaboration among team members but also creates opportunities for coaching and learning with every analysis. Pre-built investigations and facets (sequences of questions) on the platform help teams build best practices and speed up future investigations – contributing to continues efficiency improvements through institutional knowledge.
Final thoughts
Operationalizing threat intelligence is a complex but critical task for security operations teams. Command Zero is designed to simplify this process, enabling teams to act quickly, efficiently, and consistently. By addressing the challenges of volume, prioritization, and actionability, Command Zero is helping SecOps teams stay one step ahead of threat actors.
As one of our customers aptly put it, “We’re still working day and night to solve these problems that have existed for 20-plus years in the industry.” So there is a lot of room for improvement in the Security Operations space. With Command Zero, the value we will all get from threat intelligence is higher than before thanks to efficient operationalization of CTI signals.
Book a demo with our team to experience how Command Zero can help your analysts operationalize threat intelligence and more.
Subscribe security updates
Run Better Investigations.
At Every Tier.