Investigating Risky Sign-ins: Getting to the right answers fast
Investigative challenges around risky sign-ins

Introduction
Account compromises are a major concern for security teams. Detecting and responding to them quickly can mean the difference between a minor incident and a major breach. In this post, I'll explain risky sign-ins, their importance in security operations, and how Command Zero helps streamline these critical investigations.
What are risky sign-ins?
Microsoft Entra ID Protection identifies "risky sign-ins" by analyzing unusual patterns in user sign-in attempts. These are login attempts that deviate from established user behavior or exhibit characteristics associated with security threats. Risky sign-ins are categorized as low, medium, or high risk, triggering alerts or actions based on those risk levels.
While Microsoft uses "risky sign-ins," other identity providers employ different terminology for similar concepts:
- Okta: "Behavior detection"
- Google: "Suspicious logins"
- AWS: "Suspicious activity" and "anomalous/unusual behavior"
Despite varying terminology, these identity providers all analyze login location, IP address, device information, access timing, authentication methods, and user behavior patterns to identify potential threats.
Detection triggers
Microsoft Entra ID Protection analyzes several factors during each sign-in attempt:
- Geographic Location: Sign-ins from atypical or unfamiliar locations
- IP Address Analysis: Logins from anonymous, malicious, or unusual IP addresses
- Device and Browser Patterns: First-time device or browser usage
- Temporal Anomalies: Sign-ins during unusual hours for the user
- Impossible Travel: Authentication from two distant locations within an implausible timeframe
- Password Spray Detection: Multiple sign-in attempts, often performed in an automated fashion using common passwords
- Leaked Credentials: Sign-in attempts using known compromised credentials
- Malicious IP Addresses: Authentication from IPs associated with known malicious activity
Microsoft categorizes these risks into three levels—low, medium, and high—allowing organizations to configure appropriate Conditional Access policies that can require additional authentication factors or block access entirely.
Management tools
Security teams can monitor and respond to risky sign-ins through several mechanisms:
- Microsoft Entra ID Protection: The core service that identifies potential authentication risks
- Risky Sign-ins Report: Administrative dashboard for monitoring and investigating suspicious logins
- Remediation Actions: Options to confirm sign-ins as compromised or safe, or dismiss the risk
- Conditional Access Integration: Automated policies that can trigger user self-remediation steps
- Risk Feedback Loop: Administrator input to improve Microsoft's risk detection algorithms
Putting risky sign-in alerts to work
Account compromise represents one of the most significant threats facing organizations today. As part of Microsoft's identity protection service, Entra's risky sign-in detections highlight abnormal login behavior that often indicates compromised credentials. These detections serve as critical early warning signals for security analysts. When properly monitored and investigated, they can reveal unauthorized access attempts before attackers gain a foothold in your environment.
Why risky sign-ins are an important signal for Security Operations
For SOC analysts, risky sign-in detections are crucial in identifying and responding to threats quickly. Let's look at some specific examples:
- Atypical Travel: One of the most common alerts involves authentication from geographically impossible locations within a short timeframe. For example, a login from Texas followed by another from Canada five minutes later is physically impossible, raising immediate red flags.
- Password Spray Attacks: Microsoft surfaces detections when successful logins are associated with password spray attempts – a technique where attackers try common passwords across numerous accounts. These detections often reveal the initial stages of a broader attack.
- Malicious IP Addresses: Sign-ins from IP addresses known to be associated with threat actors or compromised infrastructure are immediately flagged, providing a crucial early indicator of potential compromise.
Investigative challenges around risky sign-ins
The real complexity emerges during investigation. When a risky sign-in alert fires, security analysts face several critical challenges:
- Scope assessment
Understanding the full extent of a compromise is particularly difficult. If an account is truly compromised, determining which assets have been accessed and what actions were taken requires visibility across multiple systems.
- Technology fragmentation (aka security silos)
Most organizations maintain different security tools, dashboards, and directories across various technology stacks. This fragmentation forces analysts to piece together information from disparate sources – a time-consuming process that delays response.
- Context collection
Gathering the necessary context around a suspicious login often requires manual lookups across multiple systems, from identity providers to endpoint protection platforms and cloud environments.
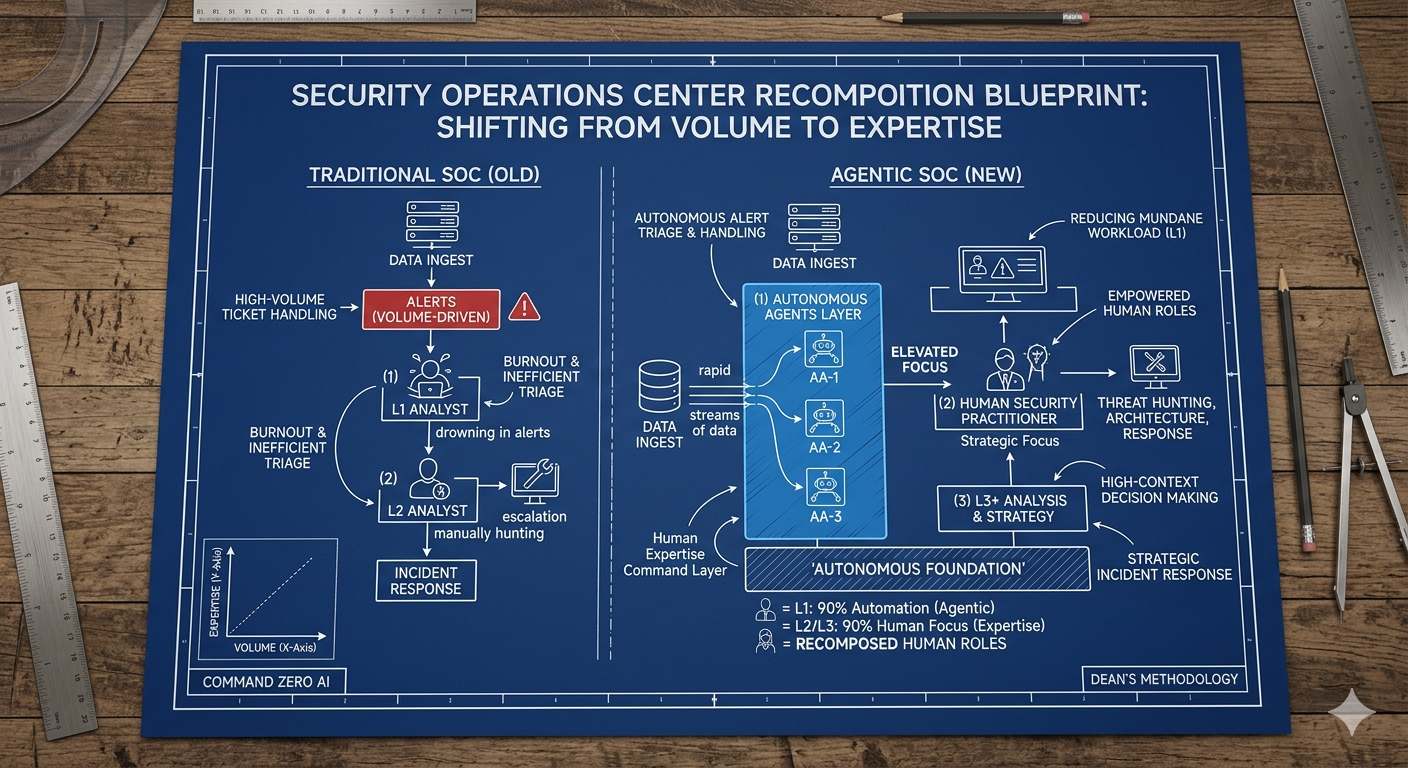
How Command Zero helps get to the right answers fast
Command Zero fundamentally transforms how security teams investigate risky sign-ins through several key capabilities:
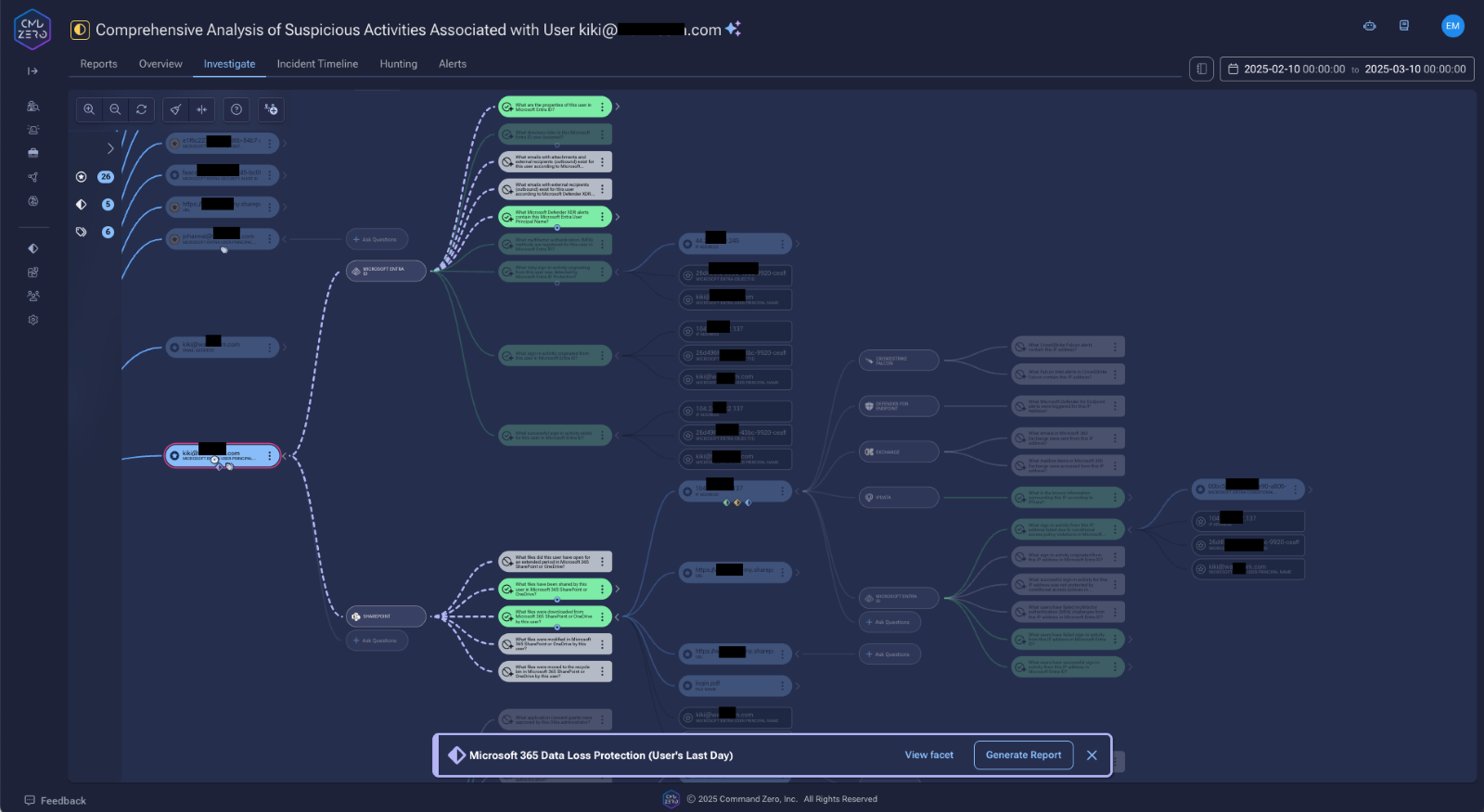
- Cross-Product visibility & enrichment
Our platform consolidates investigative capabilities into a single dashboard, enabling analysts to trace activity across Microsoft Entra ID, AWS, CrowdStrike, other security and non-security tools from a unified interface. Analysts can investigate cross-products using the encoded knowledge base in the platform, removing barriers of entry for interrogating each resource.
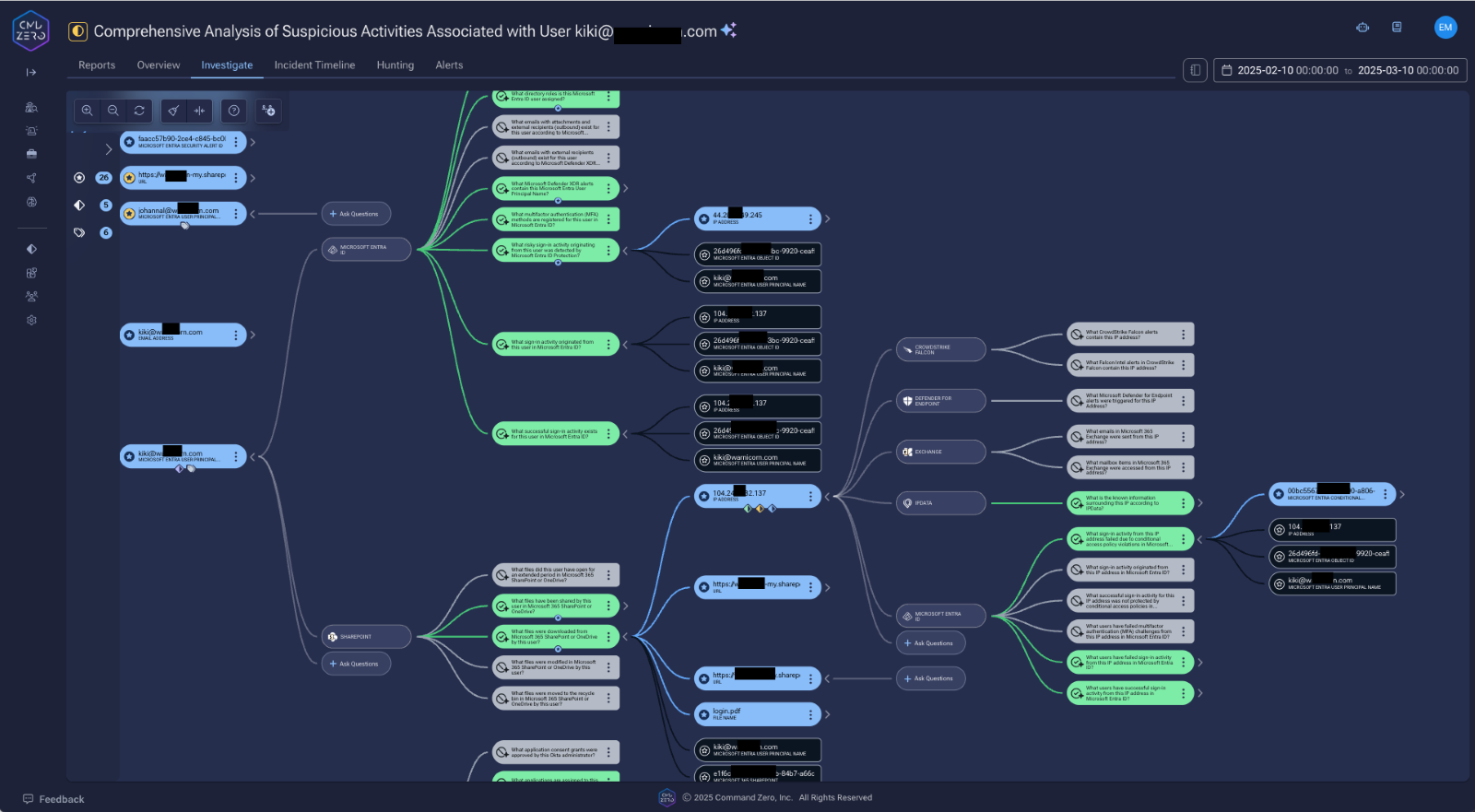
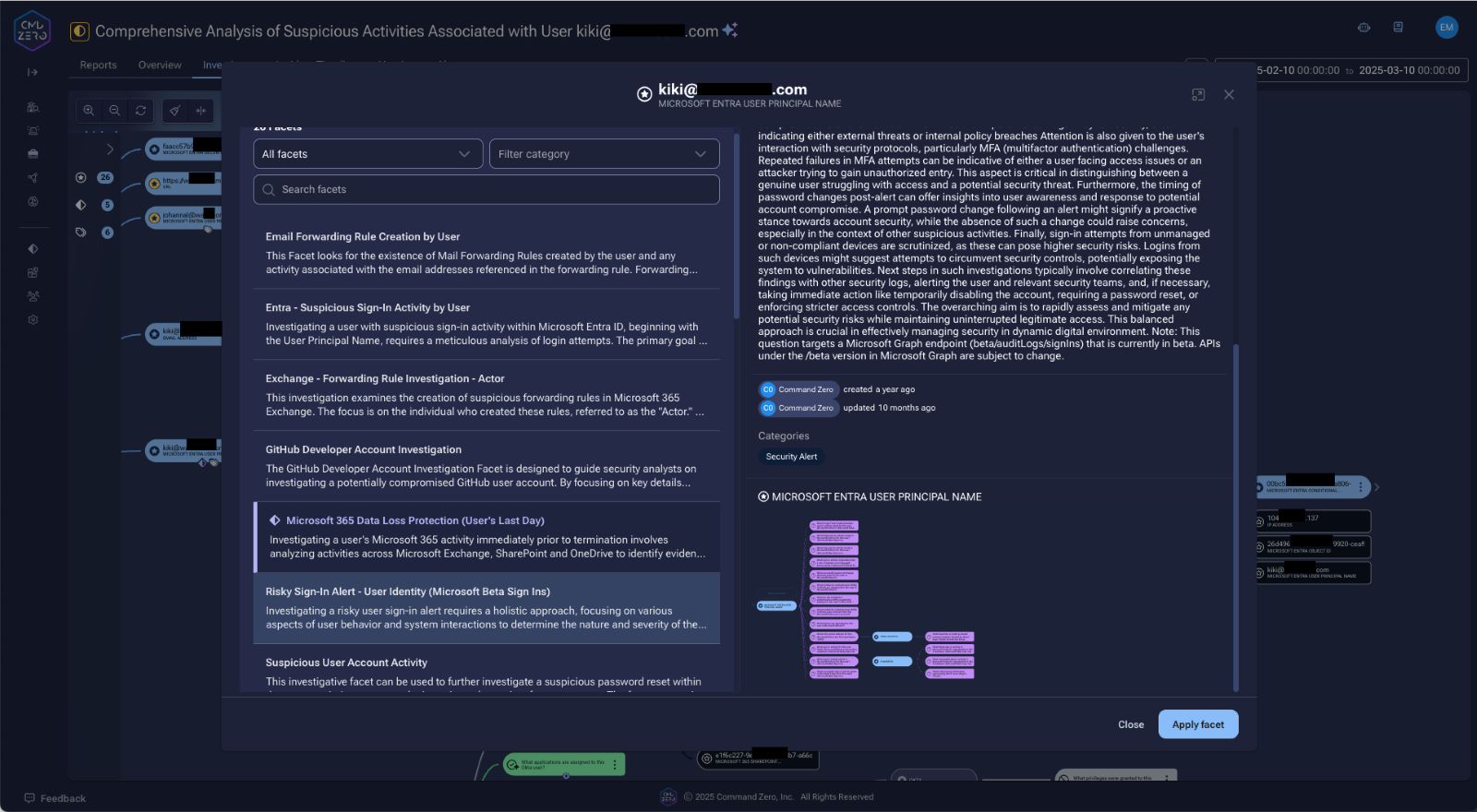
- Streamlining investigations with pre-built sequences
We've developed facets (pre-configured sequences of relevant investigative questions) that can be applied with a single click. When a suspicious IP is identified, analysts can immediately check its presence across all connected systems, dramatically accelerating the investigation process.
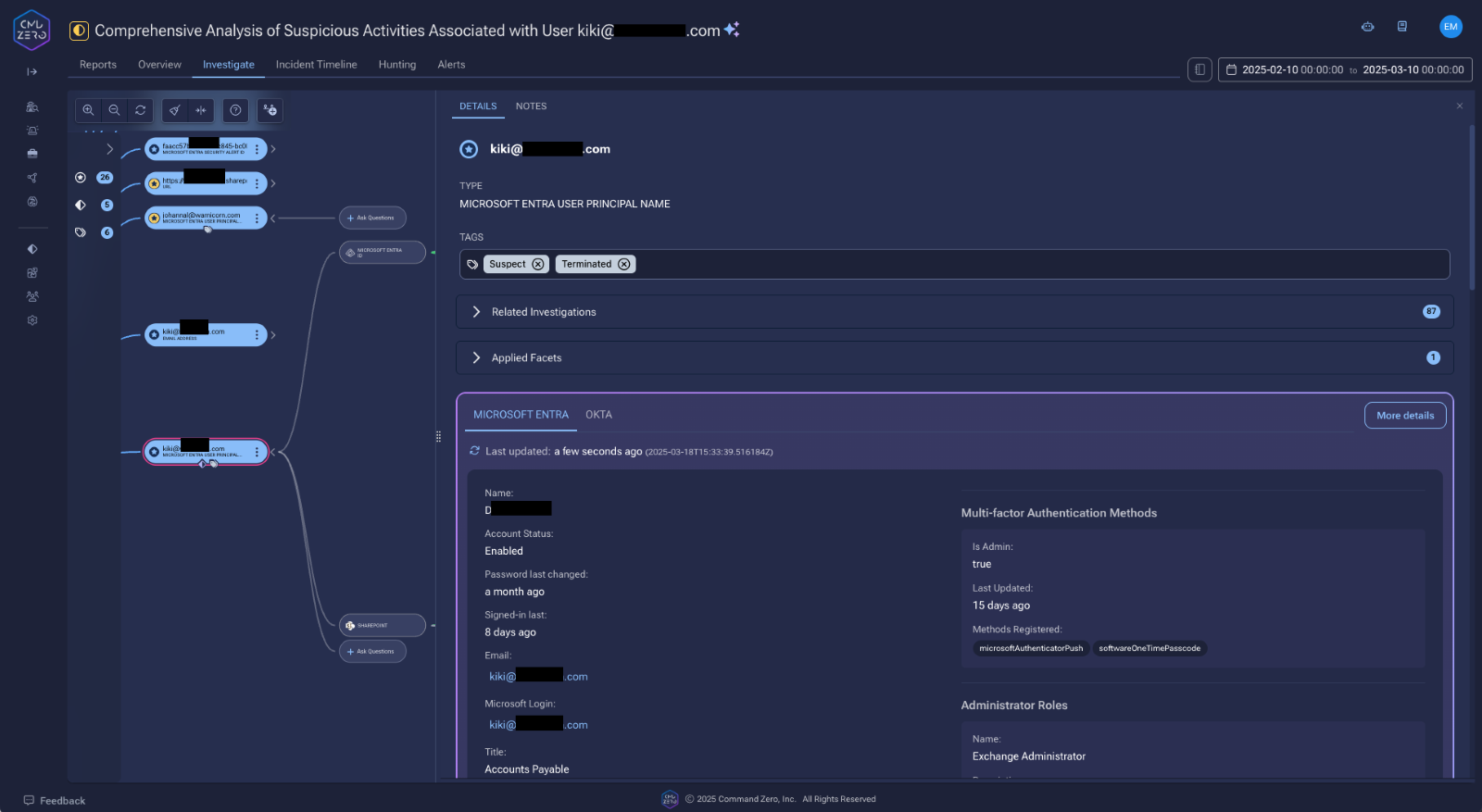
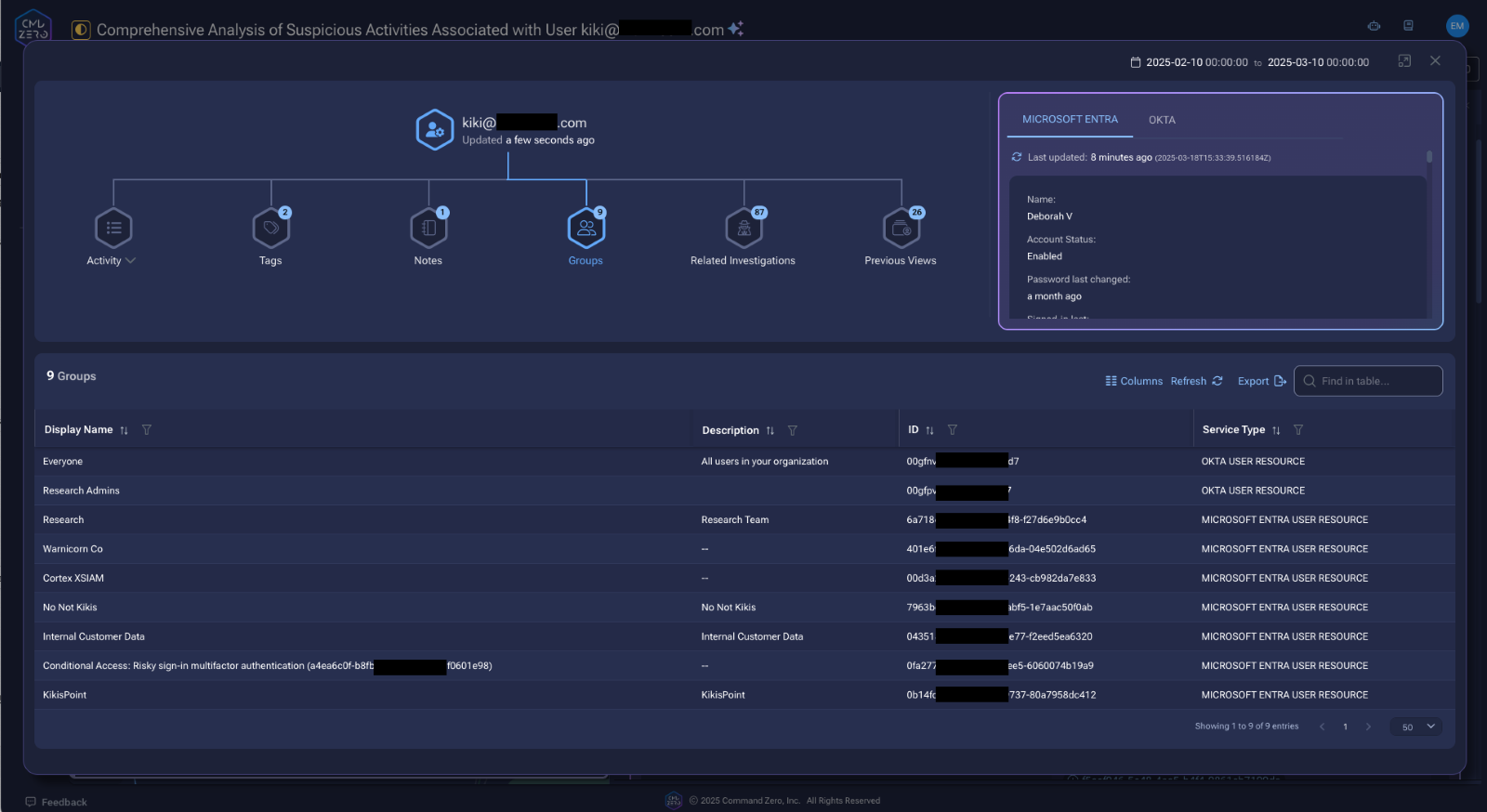
- User resource correlation
Command Zero automatically correlates identities across systems, eliminating manual directory lookups. The resource view also shows notes, tags about each user along with previous investigations that the user was involved with. An analyst investigating a potentially compromised Microsoft Entra account can instantly see the corresponding identities in Okta, GitHub, and other connected systems, along with the historical context for this lead.
- Baselines for all outcomes
Our facets establish a consistent investigative baseline that all analysts follow, ensuring investigative quality doesn't vary between team members. This standardization creates predictable, reliable outcomes while still allowing individual analysts to build upon this foundation.
- Contextual prioritization
Command Zero helps distinguish between high-priority and routine incidents by providing critical context. A super-admin logging in from an unexpected location represents a substantially different risk than an intern accessing systems from their summer house.
Conclusion
Risky sign-ins are noteworthy signals in today's identity-centric security landscape. These detection mechanisms identify authentication anomalies that signal potential credential compromise—from impossible travel patterns and password spray attacks to logins from malicious infrastructure.
As threat actors increasingly target identity systems as their primary attack vector, organizations must evolve beyond basic alerting to implement comprehensive investigation workflows that provide cross-platform visibility and contextual intelligence. By transforming how security teams respond to these critical early warning signals, we enable faster, more decisive action that prevents minor security incidents from escalating into catastrophic breaches.
The future of effective identity protection lies not merely in detection, but in the orchestrated investigative capabilities that empower security teams to rapidly understand, contain, and remediate identity-based threats before attackers can establish persistence in your environment.
What sets Command Zero apart when it comes to risky sign-in investigations are our unique combination of an encoded knowledge base, expert LLMs, and automation capabilities. This integrated approach allows for:
- Rapid Context Building: Quickly gather and correlate relevant information from across the environment.
- Intelligent Analysis: Leverage AI to identify patterns and potential threats that might be missed by traditional rule-based systems.
- Streamlined Workflow: Automate routine tasks while providing powerful tools for in-depth manual investigation when needed. Build rules to guide automation flows to tackle specific case patterns, get verdicts and full reports from autonomous investigations.
- Continuous Learning: Our system evolves with each investigation, improving its ability to detect and respond to new threats. The Command Zero security research team builds new questions and facets each week, and your teams can build their own best practices for building institutional knowledge. So, your team learns continuously and improves with every investigation.
By combining these capabilities, we've created a platform that dramatically improves the efficiency and effectiveness of risky sign-in investigations, enabling security teams to respond faster and with greater confidence to potential identity threats.
Book a demo with our team to see how Command Zero can transform Microsoft Risky Sign-in investigations and tier-2+ analysis for your organization.
Subscribe security updates
Run Better Investigations.
At Every Tier.