The Command Zero API and MCP Server Are Live
Command Zero today released a broad set of API endpoints and a Model Context Protocol (MCP) server for its Autonomous & AI-Assisted SOC platform.

SOCs consist of dozens of separate tools and need seamless connectivity to overcome complexity. With this release, teams can wire the Command Zero platform directly into their SOAR playbooks, orchestration pipelines, and internal tooling. This represents a fundamental architectural shift: investigation is no longer just a destination analysts must visit, but a callable capability embedded natively within existing automated workflows.
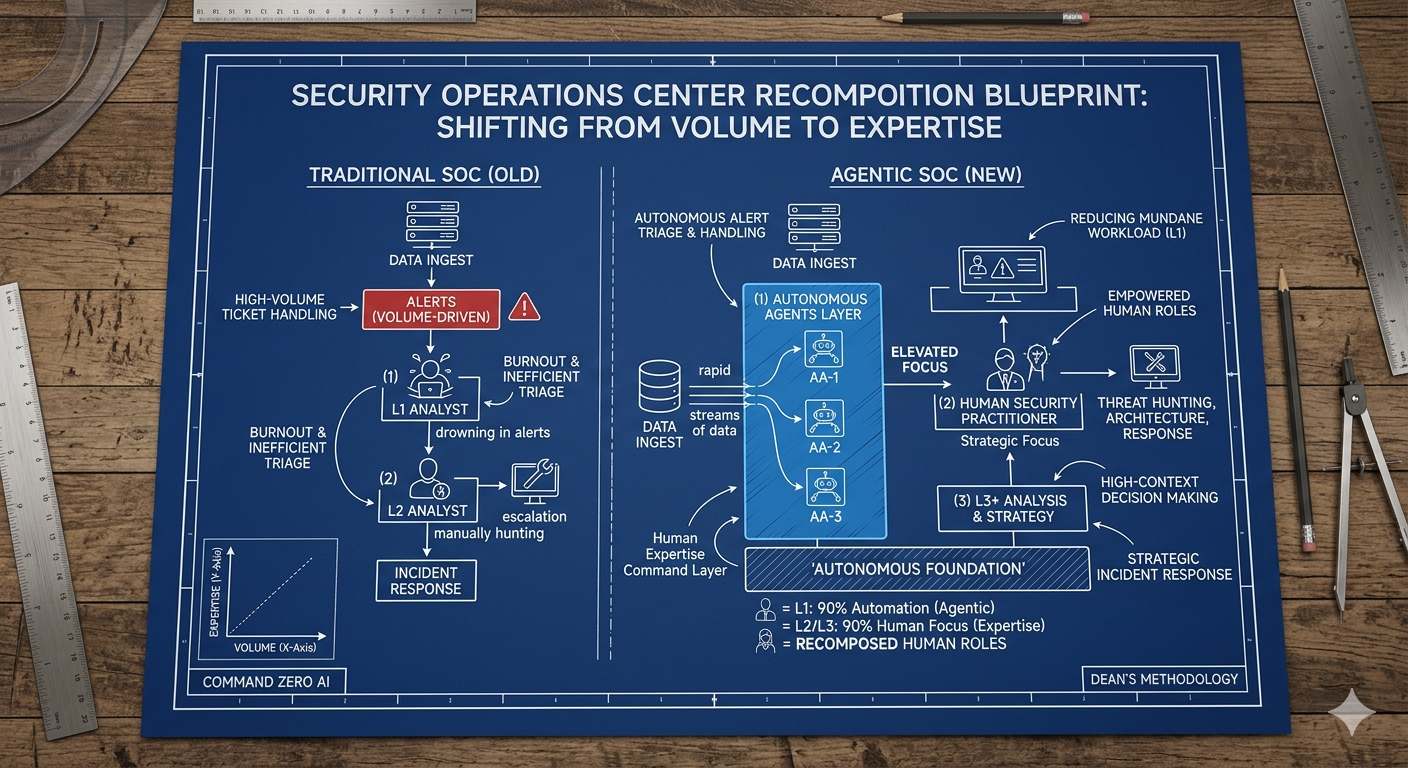
The Big Picture
This configuration ensures AI acts as an elevating force for human analysts, surfacing vital context and institutional methodology so practitioners can make faster, higher-confidence decisions without manually jumping between consoles.
What Shipped
The API is organized across seven core functional areas to drive programmatic investigations and remediation:
- Investigation APIs: List, start, extend, update, and retrieve investigations against any named template. Merging logic is built-in; related SIEM alerts consolidate into single Cases automatically.
- Business Context APIs: List, upload, and retrieve context at scale. Pull identity and asset data from ServiceNow, CTEM platforms, and HR systems to ensure investigations are context-aware from the moment they fire, eliminating manual console entry.
- Remediation APIs: List available templates and execute containment actions programmatically. Every automated action requires a justification for the audit trail, and reversible actions carry clear undo pathways.
- Catalog and Schema APIs: Query entity types and data sources to seamlessly align external systems with the platform's native data model.
The MCP Server: Natural Language Investigation
The release also includes an MCP server which serves as a wrapper around the APIs that lets Claude and other MCP-compatible agents interact with Command Zero directly.
Analysts can run health checks, list investigations, triage open Cases, and build custom dashboards directly from an AI chat interface. Through 25 tools and seven specific slash commands (like /soc-dashboard, /investigate, and /remediate), Claude orchestrates the API calls while the analyst remains firmly in the driver's seat.
The Bottom Line
Agentic capabilities elevate analysts. The automation structures the investigation and surfaces the critical context, allowing the analyst to apply expert judgment and make high-stakes decisions in minutes instead of hours.
Go Deeper
What You Can Build Today
Security teams and technical alliance partners can build integrations in minutes that fundamentally alter how their SOC operates.
- Smarter SOAR Playbooks: Trigger a Command Zero investigation the moment a SIEM alert fires. Your playbook sends alert data to the investigations endpoint, provides a postback URL, and receives structured, auditable findings when the investigation completes. The merging logic handles the noise: if multiple related alerts fire against the same sender inside a short window, they consolidate into a single investigation.
- Proactive Business Context Synchronization: Upload and sync contextual data directly from HR directories, CMDB records, and asset inventories. MSSPs managing multiple tenant environments can sync client context across their entire customer base via the API, ensuring investigations are accurate and environment-aware without manual data entry.
- Seamless Lifecycle Management: Build custom internal tools that leverage the API to list available remediation templates, execute containment actions programmatically, track execution status, and record justifications in the audit trail.
A Specific Case in the SOC: Identity Compromise
To understand the architectural shift, consider a high-fidelity alert: an identity provider flags an impossible travel event for a privileged account.
- The Old Way (Destination Investigation): A SOAR playbook enriches the IP, creates a ticket, and waits. An analyst eventually opens the ticket, logs into a separate investigation console, manually searches for the user, checks their access levels, and spends 30 minutes gathering context before making a decision.
- The Command Zero Way (Callable Investigation): The SOAR playbook catches the alert and instantly hits the Command Zero API. Because HR and CMDB data are synced via the Business Context API, the platform already knows this account belongs to a VP of Engineering with access to production databases.
- Exploring the Dossier: The automated investigation instantly explores the distinct Facets of this identity's dossier: What non-human identities are tied to this account? What is the blast radius? Has this identity been observed in prior alerts?
- The Analyst is Elevated: By the time the tier-2 analyst opens the Case, the heavy lifting is done. Using the MCP server in Claude Code, the analyst runs /investigation-status to review the structured findings. Seeing a high-confidence compromise, they run /remediate, select the "Disable Account & Revoke Sessions" template, provide a justification for the audit trail, and close the Case.
What's next:
This initial release covers the core surface customers need to start building. Additional API endpoints will follow, shaped directly by feedback from anchor customers and partners. Be sure to check out Eric Hulse video overview showing a use of Claude and our new API create augmented Investigative Intelligence.
James Therrien
Command Zero today released a broad set of API endpoints and a Model Context Protocol (MCP) server for its Autonomous & AI-Assisted SOC platform.
Subscribe security updates
Run Better Investigations.
At Every Tier.